How Configure Fortigate in Transparent Mode
Thanks to: https://docs.fortinet.com/
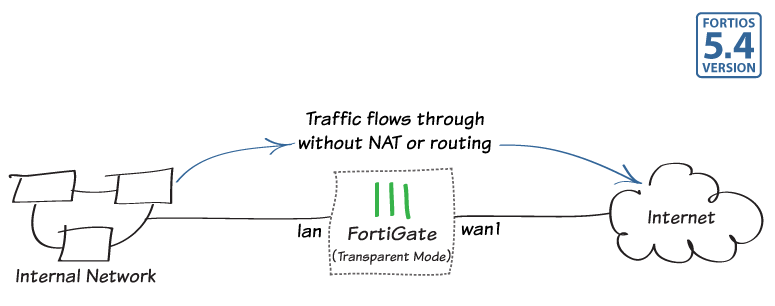
In this example, you will learn how to connect and configure a new FortiGate unit in Transparent mode to securely connect a private network to the Internet.
Transparent mode is used if you want to apply security scanning to traffic without applying routing or network address translation (NAT), such as when a FortiGate is used as an Internal Segmentation Firewall (ISFW).
1. Changing the FortiGate's operation mode
From the PC on the internal network, connect to the FortiGate's web-based manager using either FortiExplorer or an Internet browser (for information about connecting to the web-based manager, please see your models QuickStart Guide).
Login using an admin account (the default admin account has the username admin and no password).

Go to the Dashboard and enter the following command into the CLI console widget, substituting your own IP addresses where necessary:
config system settings set opmode transparent set manageip 192.168.200.111 255.255.255.0 set gateway 192.168.200.99 end
You can now access the FortiGate using the new Management IP address (in the example, https://192.168.200.111).
Go to the Dashboard. The System Information widget shows the Operation Mode is Transparent.

2. (Optional) Setting the FortiGate's DNS servers
The FortiGate unit's DNS Settings are set to use FortiGuard DNS servers by default, which is sufficient for most networks. However, if you need to change the DNS servers, go to Network > DNS, select Specify, and add Primary and Secondary DNS servers.

3. Creating a policy to allow traffic from the internal network to the Internet
Some FortiGate models include an IPv4 security policy in the default configuration. If you have one of these models, edit it to include the logging options shown below, then proceed to the results section.
Go to Policy & Objects > IPv4 Policy and create a new policy. Give the policy a Name that indicates that the policy will be for traffic to the Internet (in the example, Internet).
Set the Incoming Interface to the internal interface (called internal on some FortiGate models) and the Outgoing Interface to the Internet-facing interface (typically wan1). Set Source, Schedule, and Services as required.
Make sure the Action is set to ACCEPT.

Scroll down to view the Logging Options. In order to view the results later, enable Log Allowed Traffic and select All Sessions.

4. Connecting the network devices
Go to the Dashboard and locate the System Resources widget. Select Shutdown to power off the FortiGate unit.
Alternatively, you can enter the following command in the CLI Console:
execute shutdown
Wait until all the lights, except for the power light, on your FortiGate have turned off. If your FortiGate has a power button, use it to turn the unit off. Otherwise, unplug the unit.
You can now connect the FortiGate unit between the internal network and the router.
Connect the wan1 interface to the router internal interface and connect the internal network to the FortiGate internal interface port.

Power on the FortiGate unit.
5. Results
You can now browse the Internet using any computer that connects to the FortiGate's internal interface.
You can view information about the traffic being processed by your FortiGate by going to FortiView > All Sessions and selecting the now view.
Select Add Filter and filter for Policy, selecting the name of your new policy. Only traffic flowing through the new policy is displayed.



Comentarios
Publicar un comentario
Dime si la información de este blog te sirvio.